New Release of the video chat:
Added Features:
- Fixed some bugs
- Improved error handling
- Added NAT Holepunch Capability (explained below)
- Added HTTP Tunneling Capability (explained below)
NAT Holepunch or HTTP Tunneling.
The techniques worked in following situations:
- Direct connection from a host (me) to a virtual machine on the host and vice versa
- Software Firewalls enabled
- In case of NAT Holepunch, I ran the relay server on the host and used two virtual machines which communicated with each other
NAT Holepunch:
Participants:
- A relay server with open udp ports
- One computer behind a NAT
- Another computer behind a NAT
NAT: Network address translation
--> means ports are forwarded to the device behind it and vice versa from the device to other devices
Problem: A lot of NAT devices permit receiving UDP packets, but sending them.
That's why we can send packets to a server who can listen on all UDP ports and accept our request.
Principle:
At first the relay server is listening on a pre defined port for incoming udp packets.
Computer A tries to send a UDP packet to this server.
The packet contains information about connection details of the according peer Computer A would like to connect to later.

The relay server gets the packet and remembers the senders IP + UDP port and the packet content for later requests by Computer B.
Now Computer B sends a UDP packet to the relay server with connection details (e.g. IP) of his according peer, namely Computer A.
The relay server again gets this request and compares in his list of requests whether the new connection details from the packet match one from earlier saved requests.

If thats the case the server sends out to both peers each others connection details to the open ports earlier received of them.

Now Computer A sends UDP Packets on this open port to the direct peer on his open port and vice versa.
Now both can communicate.
HTTP Tunneling and HTTP Streaming
If you are behind a firewall your only way to communicate with the outer world is to use port 80, which is used for all http traffic (when you are browsing the internet).
In this case HTTP Tunneling comes into play.
Principle:
Short version:
We use HTTP to send the video stream to the other peer and vice versa. That means both parties have to have a listening webserver on port 80.
Long version:
Originally RTP Packets are sent via UDP as underlying protocoll. Due to the nature of firewalls blocking most traffic in general it is not possible to stream your UDP packets to another location.
The solution is to use the only free port (80). This opens another problem. In contrast to RTP HTTP works with TCP/IP as underlying protocoll. This means we have to deal with packet retransmission and therefore delays in the reception of the data.
HTTP Streaming
One solution would be to implement the common known HTTP Streaming. This works the way that you have split your stream in time equavilant segments and send these to a webserver, which serves these files.
Now the client connects to the webserver and reads one file after another.
Bad side of this method: It is not real time anymore. Due to the creation of the files the client has to wait at least the time the server needs to capture one segment and load it onto the webserver.
So what to do now?
Well, I tried to implement my own HTTP Streaming solution which roughly works like this:
- start capturing from the webcam
- while capturing read out the streaming bytes
- wait until a certain buffer is filled with video data
- now send this buffered data over http to the opponent webserver
- on this webserver we read out the received data and create UDP packets which are sent to the local RTP Receiver
- steps 1-5 on both sides
Result: Depending on your webcam it will work!
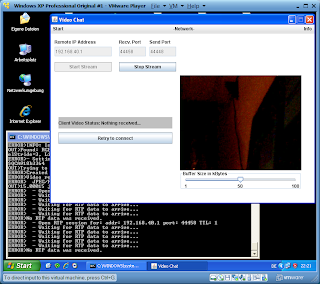
Pictures:
 Hosting peer: Left side --> received stream over HTTP Tunneling
Hosting peer: Left side --> received stream over HTTP TunnelingRight side-->webcam not working ;-)
 Virtual Machine Client peer: Right side: local webcam stream, left: no reception due to bad webcam of other peer
Virtual Machine Client peer: Right side: local webcam stream, left: no reception due to bad webcam of other peerDownload
VideoChat1.2.jar
Environment
JRE 1.6_U20 32 Bit
Windows XP 32 Bit
Windows 7 64 Bit
Hi.. I need to contact you with regarding to Audio Video Chat through Network in Java.. my email ID is Mohd_siraj2003@yahoo.com
ReplyDeletehi...could you please direct me to material which would help develop this application. I am a newbie to JMF and currently I am referring to an IBM tutorial.Also regarding your video chat, I am tryin to capture video with JMStudio and even though my device is detected I am not able to capture. I keep getting the below error
ReplyDeleteControl error : Failed to realize : input media not supported : yuv video
Please contact me at aayushberi08@gmail.com
Aayush
hii,
ReplyDeleteI am trying to develop a telemedicine software in java for which i need to establish a video chat between doctor and patient. PLz help me.
my email id is
pg.manit@gmail.com
we want the source code pleas maaaan
ReplyDeletepleas connect with me
anaaimouna@hotmail.com
your work is amazing, i sent you so many email, please please reply mine is gabriel6ft(at)yahoo.com
ReplyDeletecan you provide the source code of this? my email address is.. dhavaljoshi43@gmail.com
ReplyDeleteplease send the source code
ReplyDeleteikandigital@gmail.com
I am trying a develope java video chatting app pleaz contact me
ReplyDeletegajith.sandaruwan@gmail.com
Hi.. you have made a nice video chat app in java.
ReplyDeleteCould you please upload the source code or mail the source code at ankit.aki@gmail.com??
This comment has been removed by the author.
ReplyDeletewe are doing a tele-medicine project. We need to do video conferencing using Java. Can you send me the source code.. That will be a great help. Email : lalithaonfire@gmail.com
ReplyDeleteHello, I am doing a video Conferencing using Java, can you send me the source code.
ReplyDeleteThat wil be a great help. Email : e.nagy(at)usb-soft.com
Hi,
ReplyDeleteI am doing a video Conferencing using Java. Please send me the source code.
Email:rafiq10015@yahoo.com
Thanks
This comment has been removed by the author.
ReplyDeleteHi, I need the source code for a school project
ReplyDeleteEmail : francesco.stella97@gmail.com
thank you
Hi, I need the source code for a school project
ReplyDeleteEmail : priantorosardi@gmail.com
thank you